| Name | Last modified | Size | Description | |
|---|---|---|---|---|
| Parent Directory | - | |||
| 2014-05-16_capture-win15.biargus | 2014-08-01 16:02 | 121K | ||
| 2014-05-16_capture-win15.binetflow | 2014-08-01 16:03 | 43K | ||
| 2014-05-16_capture-win15.capinfo | 2014-08-01 15:58 | 764 | ||
| 2014-05-16_capture-win15.capinfos | 2017-01-16 10:38 | 1.1K | ||
| 2014-05-16_capture-win15.dnstop | 2017-01-16 10:38 | 3.6K | ||
| 2014-05-16_capture-win15.passivedns | 2017-01-16 10:38 | 4.0K | ||
| 2014-05-16_capture-win15.pcap | 2014-05-16 09:47 | 1.1M | ||
| 2014-05-16_capture-win15.png | 2014-08-01 16:44 | 96K | ||
| 2014-05-16_capture-win15.rrd | 2014-05-16 09:48 | 8.0M | ||
| 2014-05-16_capture-win15.tcpdstat | 2017-01-16 10:38 | 1.7K | ||
| 2014-05-16_capture-win15.weblogng | 2016-06-15 17:55 | 120K | ||
| README.html | 2014-08-01 16:48 | 5.7K | ||
| README.pdf | 2014-08-01 16:48 | 179K | ||
| README.tex | 2014-08-04 15:17 | 2.9K | ||
| bro/ | 2017-01-16 10:38 | - | ||
| fast-flux-dga-first-analysis.txt | 2017-01-16 10:38 | 4.0K | ||
Binary Used: Infected by accessing the web site www.magnetikum.cz
Details about the files used in this scenario.
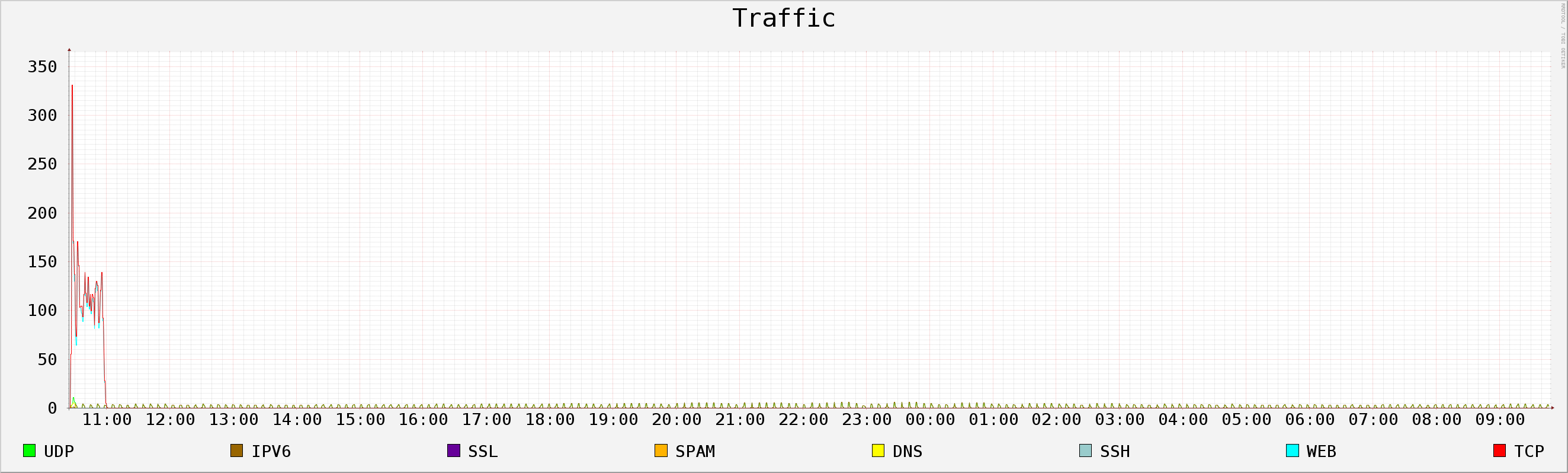
This file is a plot of the mayor features of this traffic during his whole life time.
This file is an RRD file containing all the mayor features of the traffic so you can plot it or analyze it.
This file contains the web logs of the capture extracted by the command:
These are the web logs, but each field is separated by a —.
Description of the weblogs
Thu May 15 10:24:02 CEST 2014 win15 started
Thu May 15 10:27:50 CEST 2014 infected with www.magnetikum.cz
It did not rebooted! and it access completely diferent websites!
Fri May 16 09:48:48 CEST 2014 poweroff because it was doing nothing!
File 2014-05-16_capture-win15.pcap
These files were generated as part of the Malware Capture Facility Project in the CTU University, Prague, Czech Republic. The goal of the project is to store long-lived real botnet traffic and to generate labeled netflows files. Any question feel free to contact us to sebastian.garcia@agents.fel.cvut.cz.
You are free to use these files as long as you reference this project and the authors. See http://mcfp.felk.cvut.cz